Bonjour la communauté,
Souci avec mes équipements RF, grrr… 
Depuis 1 semaine, plus de remontée d’info rf, pas d’action possible non plus.
C’est en mettant à jour le plugin que j’ai constaté le pb.
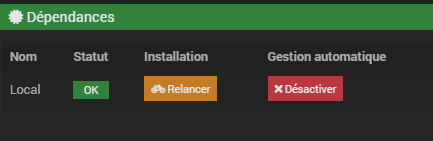
Au démarrage du plugin ça va. Quelques mn plus tard, rien ne va plus :
Msg d’erreurs Incoming packet not valid length et No decoder found pour les mêmes équipements pour qui ça allait auparavant.
Redémarrage du plugin, c’est bon, quelques mn plus tard le pb se reproduit.
J’ai testé avec RFXmngr sur PC, tout se passe bien, pas de blocage.
J’ai mis à jour le firmware du RFXCOM.
/var/www/html/plugins/rfxcom/resources/rfxcomd/rfxcomd.py --device /dev/ttyUSB0 --loglevel debug --socketport 55000 --serialrate 38400 --protocol 4,8,9,12,13,18,20,21,22,23 --callback ...
[2022-10-07 16:21:43][DEBUG] : Write data to serial port : 0d00000102000000000000000000
[2022-10-07 16:21:43][DEBUG] : Message: 1401000102532f08cc2f0003011c106e4658434f4d
[2022-10-07 16:21:43][DEBUG] : Decode : 1401000102532f08cc2f0003011c106e4658434f4d
[2022-10-07 16:21:43][DEBUG] : Test message: 1401000102532f08cc2f0003011c106e4658434f4d
[2022-10-07 16:21:43][DEBUG] : PacketType: 0x01
[2022-10-07 16:21:43][DEBUG] : Length: 21
[2022-10-07 16:21:43][DEBUG] : Start decoding packet type 0x01
[2022-10-07 16:21:43][DEBUG] : Data : {'packetlen': '0x14', 'packettype': '0x01', 'subtype': '0x00', 'seqnbr': '0x01', 'cmnd': '0x02', 'msg1': '0x53', 'msg2': '0x2F', 'msg3': '0x08', 'msg4': '0xCC', 'msg5': '0x2F', 'msg6': '0x00', 'msg7': '0x03', 'msg8': '0x01', 'msg9': 28, 'msg10': '0x10', 'msg11': '0x6E', 'msg12': '0x46', 'msg13': '0x58', 'msg14': '0x43', 'msg15': '0x4F', 'msg16': '0x4D'}
[2022-10-07 16:21:43][DEBUG] : Subtype = response on a mode command
[2022-10-07 16:21:43][DEBUG] : Firmware version = 0x2F
[2022-10-07 16:21:43][DEBUG] : RFXtrx433 operating at 433.92MHz
[2022-10-07 16:21:43][DEBUG] : Hardware major version = 0x03
[2022-10-07 16:21:43][DEBUG] : Hardware minor version = 0x01
[2022-10-07 16:21:43][DEBUG] : Output power = 10 dBm
[2022-10-07 16:21:43][DEBUG] : Firmware ProXL1
[2022-10-07 16:21:43][DEBUG] : Noise level (only used in special firmware) = 0x6E
[2022-10-07 16:21:43][DEBUG] : undec on : 0
[2022-10-07 16:21:43][DEBUG] : Imagintronix,Opus/Alecto2010/Alecto : 0
[2022-10-07 16:21:43][DEBUG] : Byron SX,SelectPlus/Alecto5500 : 0
[2022-10-07 16:21:43][DEBUG] : RSL,Revolt/La Crosse : 0
[2022-10-07 16:21:43][DEBUG] : Lighting4/Davis EU : 1
[2022-10-07 16:21:43][DEBUG] : FineOffset,Viking/Davis US : 0
[2022-10-07 16:21:43][DEBUG] : Rubicson,Alecto,Banggood/Davis AU : 0
[2022-10-07 16:21:43][DEBUG] : AE Blyss : 0
[2022-10-07 16:21:43][DEBUG] : BlindsTx : 1
[2022-10-07 16:21:43][DEBUG] : BlindsT0 : 1
[2022-10-07 16:21:43][DEBUG] : Proguard : 0
[2022-10-07 16:21:43][DEBUG] : Legrand CAD : 0
[2022-10-07 16:21:43][DEBUG] : La Crosse : 1
[2022-10-07 16:21:43][DEBUG] : Hideki,TFA,Cresta,UPM/FS20 : 1
[2022-10-07 16:21:43][DEBUG] : AD LightwaveRF : 0
[2022-10-07 16:21:43][DEBUG] : Mertik/Edisio : 0
[2022-10-07 16:21:43][DEBUG] : Visonic : 0
[2022-10-07 16:21:43][DEBUG] : ATI/cartelectronic/Meiantech,Atlantic : 0
[2022-10-07 16:21:43][DEBUG] : Oregon Scientific/Keeloq : 1
[2022-10-07 16:21:43][DEBUG] : Meiantech,Atlantic/Proguard : 0
[2022-10-07 16:21:43][DEBUG] : HomeEasy EU : 1
[2022-10-07 16:21:43][DEBUG] : AC : 1
[2022-10-07 16:21:43][DEBUG] : ARC : 1
[2022-10-07 16:21:43][DEBUG] : X10 : 1
[2022-10-07 16:21:43][DEBUG] : FunkBus 433.42/Itho CVE RFT : 0
[2022-10-07 16:21:43][DEBUG] : MCZ 434.50/Itho CVE ECO RFT : 0
[2022-10-07 16:21:43][DEBUG] : Honeywell Chime : 0
[2022-10-07 16:21:43][DEBUG] : HomeConfort,Fan : 0
[2022-10-07 16:21:43][DEBUG] : Keeloq : 0
[2022-10-07 16:21:43][DEBUG] : Client connected to [127.0.0.1:55114]
[2022-10-07 16:21:43][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"A31D29"}}'
[2022-10-07 16:21:43][DEBUG] : Client disconnected from [127.0.0.1:55114]
[2022-10-07 16:21:43][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:21:43][DEBUG] : Add device : {'id': 'A31D29'}
[2022-10-07 16:21:43][INFO] : Démon RFXcom lancé
[2022-10-07 16:21:43][DEBUG] : Client connected to [127.0.0.1:55116]
[2022-10-07 16:21:43][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"6F3479"}}'
[2022-10-07 16:21:43][DEBUG] : Client disconnected from [127.0.0.1:55116]
[2022-10-07 16:21:43][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:21:43][DEBUG] : Add device : {'id': '6F3479'}
[2022-10-07 16:21:44][DEBUG] : msg3: [0, 0, 0, 0, 1, 0, 0, 0] / 08
[2022-10-07 16:21:44][DEBUG] : msg4: [1, 1, 0, 0, 1, 1, 0, 0] / cc
[2022-10-07 16:21:44][DEBUG] : msg5: [0, 0, 1, 0, 1, 1, 1, 1] / 2f
[2022-10-07 16:21:44][DEBUG] : msg6: [0, 0, 0, 0, 0, 0, 0, 0] / 00
[2022-10-07 16:21:44][DEBUG] : Command: 0d00000203531C08cc2f00000000
[2022-10-07 16:21:44][DEBUG] : Protocol actually activated 08cc2f00
[2022-10-07 16:21:44][DEBUG] : Actual Frequency 53
[2022-10-07 16:21:44][DEBUG] : Wanted protocol 08cc2f00
[2022-10-07 16:21:44][DEBUG] : All is ok, sending start
[2022-10-07 16:21:44][DEBUG] : Write data to serial port : 0d00000207000000000000000000
[2022-10-07 16:21:44][DEBUG] : Message: 1401070207436f7079726967687420524658434f4d
[2022-10-07 16:21:44][DEBUG] : Decode : 1401070207436f7079726967687420524658434f4d
[2022-10-07 16:21:44][DEBUG] : Test message: 1401070207436f7079726967687420524658434f4d
[2022-10-07 16:21:44][DEBUG] : PacketType: 0x01
[2022-10-07 16:21:44][DEBUG] : Length: 21
[2022-10-07 16:21:44][DEBUG] : Start decoding packet type 0x01
[2022-10-07 16:21:44][DEBUG] : Data : {'packetlen': '0x14', 'packettype': '0x01', 'subtype': '0x07', 'seqnbr': '0x02', 'cmnd': '0x07', 'msg1': '0x43', 'msg2': '0x6F', 'msg3': '0x70', 'msg4': '0x79', 'msg5': '0x72', 'msg6': '0x69', 'msg7': '0x67', 'msg8': '0x68', 'msg9': 116, 'msg10': '0x20', 'msg11': '0x52', 'msg12': '0x46', 'msg13': '0x58', 'msg14': '0x43', 'msg15': '0x4F', 'msg16': '0x4D'}
[2022-10-07 16:21:44][DEBUG] : Subtype = start RFXtrx receiver
[2022-10-07 16:22:04][DEBUG] : Client connected to [127.0.0.1:55134]
[2022-10-07 16:22:04][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"include_mode","state":"1"}'
[2022-10-07 16:22:04][DEBUG] : Client disconnected from [127.0.0.1:55134]
[2022-10-07 16:22:04][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:22:04][DEBUG] : Enter in include mode
[2022-10-07 16:22:04][DEBUG] : Send to jeedom : {'include_mode': '1'}
[2022-10-07 16:22:04][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:04][DEBUG] : {"include_mode":"1"}
[2022-10-07 16:22:04][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:08][DEBUG] : Message: 082000005d1c600669
[2022-10-07 16:22:08][DEBUG] : Decode : 082000005d1c600669
[2022-10-07 16:22:08][DEBUG] : Test message: 082000005d1c600669
[2022-10-07 16:22:08][DEBUG] : PacketType: 0x20
[2022-10-07 16:22:08][DEBUG] : Length: 9
[2022-10-07 16:22:08][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:22:08][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:22:08][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x00', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 6, 'battery': 9, 'rssi': 6}
[2022-10-07 16:22:08][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 6, 'battery': 9, 'rssi': 6}
[2022-10-07 16:22:08][DEBUG] : unknown device id : 5D1C60
[2022-10-07 16:22:08][DEBUG] : Send to jeedom : {'include_mode': 0}
[2022-10-07 16:22:08][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:22:08][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:08][DEBUG] : {"include_mode":0}
[2022-10-07 16:22:08][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 6, 'battery': 9, 'rssi': 6}}}
[2022-10-07 16:22:08][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:08][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:08][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":6,"battery":9,"rssi":6}}}
[2022-10-07 16:22:10][DEBUG] : Client connected to [127.0.0.1:55146]
[2022-10-07 16:22:10][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"5D1C60"}}'
[2022-10-07 16:22:10][DEBUG] : Client disconnected from [127.0.0.1:55146]
[2022-10-07 16:22:10][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:22:10][DEBUG] : Add device : {'id': '5D1C60'}
[2022-10-07 16:22:10][DEBUG] : Client connected to [127.0.0.1:55148]
[2022-10-07 16:22:10][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"5D1C60"}}'
[2022-10-07 16:22:10][DEBUG] : Client disconnected from [127.0.0.1:55148]
[2022-10-07 16:22:10][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:22:10][DEBUG] : Add device : {'id': '5D1C60'}
[2022-10-07 16:22:12][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:21][DEBUG] : Message: 082000015d1c600979
[2022-10-07 16:22:21][DEBUG] : Decode : 082000015d1c600979
[2022-10-07 16:22:21][DEBUG] : Test message: 082000015d1c600979
[2022-10-07 16:22:21][DEBUG] : PacketType: 0x20
[2022-10-07 16:22:21][DEBUG] : Length: 9
[2022-10-07 16:22:21][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:22:21][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:22:21][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x01', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 9, 'battery': 9, 'rssi': 7}
[2022-10-07 16:22:21][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 9, 'battery': 9, 'rssi': 7}
[2022-10-07 16:22:21][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:22:21][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 9, 'battery': 9, 'rssi': 7}}}
[2022-10-07 16:22:21][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:21][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":9,"battery":9,"rssi":7}}}
[2022-10-07 16:22:21][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:23][DEBUG] : Message: 09130002a31d29018060
[2022-10-07 16:22:23][DEBUG] : Decode : 09130002a31d29018060
[2022-10-07 16:22:23][DEBUG] : Test message: 09130002a31d29018060
[2022-10-07 16:22:23][DEBUG] : PacketType: 0x13
[2022-10-07 16:22:23][DEBUG] : Length: 10
[2022-10-07 16:22:23][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:22:23][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:22:23][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x02', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 384, 'filler': 0, 'rssi': 6}
[2022-10-07 16:22:23][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}
[2022-10-07 16:22:23][DEBUG] : Device is known id : A31D29
[2022-10-07 16:22:23][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}}}
[2022-10-07 16:22:23][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:23][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1536,"rssi":6}}}
[2022-10-07 16:22:23][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:29][DEBUG] : Message: 09130003a31d29018060
[2022-10-07 16:22:29][DEBUG] : Decode : 09130003a31d29018060
[2022-10-07 16:22:29][DEBUG] : Test message: 09130003a31d29018060
[2022-10-07 16:22:29][DEBUG] : PacketType: 0x13
[2022-10-07 16:22:29][DEBUG] : Length: 10
[2022-10-07 16:22:29][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:22:29][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:22:29][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x03', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 384, 'filler': 0, 'rssi': 6}
[2022-10-07 16:22:29][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}
[2022-10-07 16:22:29][DEBUG] : Device is known id : A31D29
[2022-10-07 16:22:29][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}}}
[2022-10-07 16:22:29][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:29][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1536,"rssi":6}}}
[2022-10-07 16:22:30][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:35][DEBUG] : Message: 09130004a31d29018060
[2022-10-07 16:22:35][DEBUG] : Decode : 09130004a31d29018060
[2022-10-07 16:22:35][DEBUG] : Test message: 09130004a31d29018060
[2022-10-07 16:22:35][DEBUG] : PacketType: 0x13
[2022-10-07 16:22:35][DEBUG] : Length: 10
[2022-10-07 16:22:35][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:22:35][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:22:35][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x04', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 384, 'filler': 0, 'rssi': 6}
[2022-10-07 16:22:35][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}
[2022-10-07 16:22:35][DEBUG] : Device is known id : A31D29
[2022-10-07 16:22:36][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 6}}}
[2022-10-07 16:22:36][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:36][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1536,"rssi":6}}}
[2022-10-07 16:22:36][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:45][DEBUG] : Message: 09130005a31d29018160
[2022-10-07 16:22:45][DEBUG] : Decode : 09130005a31d29018160
[2022-10-07 16:22:45][DEBUG] : Test message: 09130005a31d29018160
[2022-10-07 16:22:45][DEBUG] : PacketType: 0x13
[2022-10-07 16:22:45][DEBUG] : Length: 10
[2022-10-07 16:22:45][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:22:45][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:22:45][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x05', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 385, 'filler': 0, 'rssi': 6}
[2022-10-07 16:22:45][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1540, 'rssi': 6}
[2022-10-07 16:22:45][DEBUG] : Device is known id : A31D29
[2022-10-07 16:22:45][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1540, 'rssi': 6}}}
[2022-10-07 16:22:45][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:45][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1540,"rssi":6}}}
[2022-10-07 16:22:45][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:22:51][DEBUG] : Message: 09130006a31d29018170
[2022-10-07 16:22:51][DEBUG] : Decode : 09130006a31d29018170
[2022-10-07 16:22:51][DEBUG] : Test message: 09130006a31d29018170
[2022-10-07 16:22:51][DEBUG] : PacketType: 0x13
[2022-10-07 16:22:51][DEBUG] : Length: 10
[2022-10-07 16:22:51][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:22:51][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:22:51][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x06', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 385, 'filler': 0, 'rssi': 7}
[2022-10-07 16:22:51][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1540, 'rssi': 7}
[2022-10-07 16:22:51][DEBUG] : Device is known id : A31D29
[2022-10-07 16:22:51][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1540, 'rssi': 7}}}
[2022-10-07 16:22:51][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:22:51][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:09][DEBUG] : Message: 09130007a31d29018070
[2022-10-07 16:23:09][DEBUG] : Decode : 09130007a31d29018070
[2022-10-07 16:23:09][DEBUG] : Test message: 09130007a31d29018070
[2022-10-07 16:23:09][DEBUG] : PacketType: 0x13
[2022-10-07 16:23:09][DEBUG] : Length: 10
[2022-10-07 16:23:09][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:23:09][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:23:09][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x07', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 384, 'filler': 0, 'rssi': 7}
[2022-10-07 16:23:09][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 7}
[2022-10-07 16:23:09][DEBUG] : Device is known id : A31D29
[2022-10-07 16:23:09][DEBUG] : Client connected to [127.0.0.1:55204]
[2022-10-07 16:23:09][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"5D1C60"}}'
[2022-10-07 16:23:09][DEBUG] : Client disconnected from [127.0.0.1:55204]
[2022-10-07 16:23:09][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:23:09][DEBUG] : Add device : {'id': '5D1C60'}
[2022-10-07 16:23:09][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 7}}}
[2022-10-07 16:23:09][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:23:09][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1536,"rssi":7}}}
[2022-10-07 16:23:09][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:23][DEBUG] : Message: 082000085d1c600979
[2022-10-07 16:23:23][DEBUG] : Decode : 082000085d1c600979
[2022-10-07 16:23:23][DEBUG] : Test message: 082000085d1c600979
[2022-10-07 16:23:23][DEBUG] : PacketType: 0x20
[2022-10-07 16:23:23][DEBUG] : Length: 9
[2022-10-07 16:23:23][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:23:23][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:23:23][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x08', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 9, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:23][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 9, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:23][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:23:23][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 9, 'battery': 9, 'rssi': 7}}}
[2022-10-07 16:23:23][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:23:23][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":9,"battery":9,"rssi":7}}}
[2022-10-07 16:23:23][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:27][DEBUG] : Message: 082000095d1c600679
[2022-10-07 16:23:27][DEBUG] : Decode : 082000095d1c600679
[2022-10-07 16:23:27][DEBUG] : Test message: 082000095d1c600679
[2022-10-07 16:23:27][DEBUG] : PacketType: 0x20
[2022-10-07 16:23:27][DEBUG] : Length: 9
[2022-10-07 16:23:27][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:23:27][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:23:27][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x09', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 6, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:27][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 6, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:27][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:23:27][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 6, 'battery': 9, 'rssi': 7}}}
[2022-10-07 16:23:27][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:23:27][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":6,"battery":9,"rssi":7}}}
[2022-10-07 16:23:28][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:33][DEBUG] : Message: 0820000a5d1c600d79
[2022-10-07 16:23:33][DEBUG] : Decode : 0820000a5d1c600d79
[2022-10-07 16:23:33][DEBUG] : Test message: 0820000a5d1c600d79
[2022-10-07 16:23:33][DEBUG] : PacketType: 0x20
[2022-10-07 16:23:33][DEBUG] : Length: 9
[2022-10-07 16:23:33][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:23:33][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:23:33][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x0A', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 13, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:33][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 13, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:33][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:23:33][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 13, 'battery': 9, 'rssi': 7}}}
[2022-10-07 16:23:33][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:23:33][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":13,"battery":9,"rssi":7}}}
[2022-10-07 16:23:33][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:38][DEBUG] : Message: 0820000b5d1c600b79
[2022-10-07 16:23:38][DEBUG] : Decode : 0820000b5d1c600b79
[2022-10-07 16:23:38][DEBUG] : Test message: 0820000b5d1c600b79
[2022-10-07 16:23:38][DEBUG] : PacketType: 0x20
[2022-10-07 16:23:38][DEBUG] : Length: 9
[2022-10-07 16:23:38][DEBUG] : Start decoding packet type 0x20
[2022-10-07 16:23:38][DEBUG] : Subtype = X10 security door/window sensor
[2022-10-07 16:23:38][DEBUG] : Data : {'packetlen': '0x08', 'packettype': '0x20', 'subtype': '0x00', 'seqnbr': '0x0B', 'id1': '0x5D', 'id2': '0x1C', 'id3': '0x60', 'status': 11, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:38][DEBUG] : Decoded info : {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 11, 'battery': 9, 'rssi': 7}
[2022-10-07 16:23:38][DEBUG] : Device is known id : 5D1C60
[2022-10-07 16:23:38][DEBUG] : Send to jeedom : {'devices': {'5D1C6020': {'packettype': '0x20', 'subtype': '0x00', 'id': '5D1C60', 'status': 11, 'battery': 9, 'rssi': 7}}}
[2022-10-07 16:23:38][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:23:38][DEBUG] : {"devices":{"5D1C6020":{"packettype":"0x20","subtype":"0x00","id":"5D1C60","status":11,"battery":9,"rssi":7}}}
[2022-10-07 16:23:38][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:23:58][DEBUG] : Client connected to [127.0.0.1:55256]
[2022-10-07 16:23:58][DEBUG] : Message read from socket: b'{"apikey":"QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN","cmd":"add","device":{"id":"5D1C60"}}'
[2022-10-07 16:23:58][DEBUG] : Client disconnected from [127.0.0.1:55256]
[2022-10-07 16:23:58][DEBUG] : Message received in socket JEEDOM_SOCKET_MESSAGE
[2022-10-07 16:23:58][DEBUG] : Add device : {'id': '5D1C60'}
[2022-10-07 16:24:14][DEBUG] : Message: 0913000c6f3479017f60
[2022-10-07 16:24:14][DEBUG] : Decode : 0913000c6f3479017f60
[2022-10-07 16:24:14][DEBUG] : Test message: 0913000c6f3479017f60
[2022-10-07 16:24:14][DEBUG] : PacketType: 0x13
[2022-10-07 16:24:14][DEBUG] : Length: 10
[2022-10-07 16:24:14][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:24:14][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:24:14][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x0C', 'cmd1': '0x6F', 'cmd2': '0x34', 'cmd3': '0x79', 'pulse': 383, 'filler': 0, 'rssi': 6}
[2022-10-07 16:24:14][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': '6F3479', 'pulse': 1532, 'rssi': 6}
[2022-10-07 16:24:14][DEBUG] : Device is known id : 6F3479
[2022-10-07 16:24:14][DEBUG] : Send to jeedom : {'devices': {'6F347913': {'packettype': '0x13', 'subtype': '0x00', 'id': '6F3479', 'pulse': 1532, 'rssi': 6}}}
[2022-10-07 16:24:14][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:24:14][DEBUG] : {"devices":{"6F347913":{"packettype":"0x13","subtype":"0x00","id":"6F3479","pulse":1532,"rssi":6}}}
[2022-10-07 16:24:14][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:24:25][DEBUG] : Message: 0913000da31d29018070
[2022-10-07 16:24:25][DEBUG] : Decode : 0913000da31d29018070
[2022-10-07 16:24:25][DEBUG] : Test message: 0913000da31d29018070
[2022-10-07 16:24:25][DEBUG] : PacketType: 0x13
[2022-10-07 16:24:25][DEBUG] : Length: 10
[2022-10-07 16:24:25][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:24:25][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:24:25][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x0D', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 384, 'filler': 0, 'rssi': 7}
[2022-10-07 16:24:25][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 7}
[2022-10-07 16:24:25][DEBUG] : Device is known id : A31D29
[2022-10-07 16:24:25][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1536, 'rssi': 7}}}
[2022-10-07 16:24:25][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:24:25][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1536,"rssi":7}}}
[2022-10-07 16:24:25][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:24:34][DEBUG] : Message: 0913000ea31d29017f60
[2022-10-07 16:24:34][DEBUG] : Decode : 0913000ea31d29017f60
[2022-10-07 16:24:34][DEBUG] : Test message: 0913000ea31d29017f60
[2022-10-07 16:24:34][DEBUG] : PacketType: 0x13
[2022-10-07 16:24:34][DEBUG] : Length: 10
[2022-10-07 16:24:34][DEBUG] : Start decoding packet type 0x13
[2022-10-07 16:24:34][DEBUG] : Subtype = PT2262, EV1527 433.92MHz
[2022-10-07 16:24:34][DEBUG] : Data : {'packetlen': '0x09', 'packettype': '0x13', 'subtype': '0x00', 'seqnbr': '0x0E', 'cmd1': '0xA3', 'cmd2': '0x1D', 'cmd3': '0x29', 'pulse': 383, 'filler': 0, 'rssi': 6}
[2022-10-07 16:24:34][DEBUG] : Decoded info : {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1532, 'rssi': 6}
[2022-10-07 16:24:34][DEBUG] : Device is known id : A31D29
[2022-10-07 16:24:34][DEBUG] : Send to jeedom : {'devices': {'A31D2913': {'packettype': '0x13', 'subtype': '0x00', 'id': 'A31D29', 'pulse': 1532, 'rssi': 6}}}
[2022-10-07 16:24:34][DEBUG] : Starting new HTTP connection (1): 127.0.0.1:80
[2022-10-07 16:24:34][DEBUG] : {"devices":{"A31D2913":{"packettype":"0x13","subtype":"0x00","id":"A31D29","pulse":1532,"rssi":6}}}
[2022-10-07 16:24:35][DEBUG] : http://127.0.0.1:80 "POST /plugins/rfxcom/core/php/jeeRfxcom.php?apikey=QMHOGWMUxpU8JxwSCLw3cbwtHmjjZsHs75VaW4uYfv9s08pKVeARnA31hVGRYlkN HTTP/1.1" 200 0
[2022-10-07 16:25:22][DEBUG] : Message: 1c0e80fc708000fc00fcfc0e703f38e01c000000fc000000e0000000fc
[2022-10-07 16:25:22][DEBUG] : Decode : 1c0e80fc708000fc00fcfc0e703f38e01c000000fc000000e0000000fc
[2022-10-07 16:25:22][DEBUG] : Test message: 1c0e80fc708000fc00fcfc0e703f38e01c000000fc000000e0000000fc
[2022-10-07 16:25:22][DEBUG] : PacketType: 0x0E
[2022-10-07 16:25:22][DEBUG] : Length: 29
[2022-10-07 16:25:22][DEBUG] : No decoder found
[2022-10-07 16:26:08][DEBUG] : Message: fc0e703f38001c0e0000fc1c0c80fc7080001c7080fcfc0e703f38e01c001c8efc00fc000000e000e07080fcfc0e703f38001c0e0000fc1c0e80fc708000fc7080fcfc0e703f38e01c00fcfe1c00fc000000e000001c70fefc0e703f38001c0e0000fc1c0e80fc7080001c1c70fefc0e703f38e01c00001c00fc000000e000e01c70fefc0e703f38001c0e0000fc1c0e80fc708000fc1c707ec0fc8e001c8ee00e00fc1c00fc1c0e80fc7080000000fc80fc8e001c8ee00e000000fc1c0e80fc7080001c7e80fc80fc8e001c8ee00e000000fc000000e0700ec0e07e8000fcfc00e00e8ee0001cfefc1c0e80fc708000fc7e80fc80fc8e001c8ee00e
[2022-10-07 16:26:08][ERROR] : Error: Incoming packet not valid length (fc0e703f38001c0e0000fc1c0c80fc7080001c7080fcfc0e703f38e01c001c8efc00fc000000e000e07080fcfc0e703f38001c0e0000fc1c0e80fc708000fc7080fcfc0e703f38e01c00fcfe1c00fc000000e000001c70fefc0e703f38001c0e0000fc1c0e80fc7080001c1c70fefc0e703f38e01c00001c00fc000000e000e01c70fefc0e703f38001c0e0000fc1c0e80fc708000fc1c707ec0fc8e001c8ee00e00fc1c00fc1c0e80fc7080000000fc80fc8e001c8ee00e000000fc1c0e80fc7080001c7e80fc80fc8e001c8ee00e000000fc000000e0700ec0e07e8000fcfc00e00e8ee0001cfefc1c0e80fc708000fc7e80fc80fc8e001c8ee00e).
[2022-10-07 16:26:08][DEBUG] : Message: 00
Pas de souci sur les autres plugin.
J’ai lu qu’il pouvait y avoir des soucis d’environnement J’ai changé de port usb, de câble.
Merci pour votre aide 
Didier
Config :
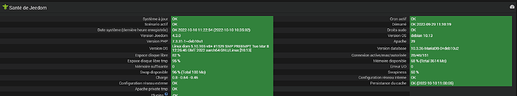
raspberry PI4, Raspbian GNU/Linux 10 (buster) / jeedom 4.2.21 / Plugin RFXCOM : 2022-09-27 01:02:45
RFXtrx433XL / Firmware 1047
Equipements rf : télécommandes alarme, détecteurs de mouvement, porte, 2 volets roulant Somfy RTS ( je les ai supprimés, je dois refaire l’appairage).